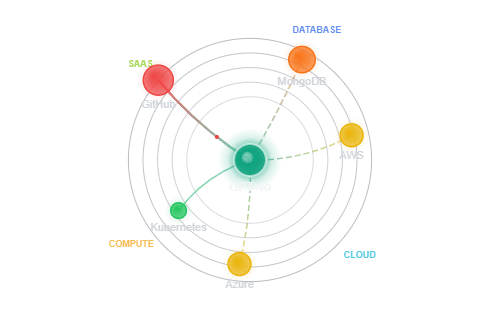
Agentic Privilege Access built for your current and future environments
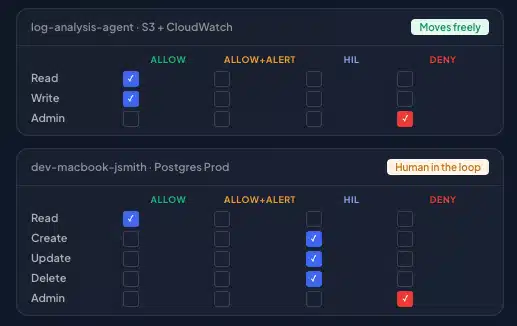
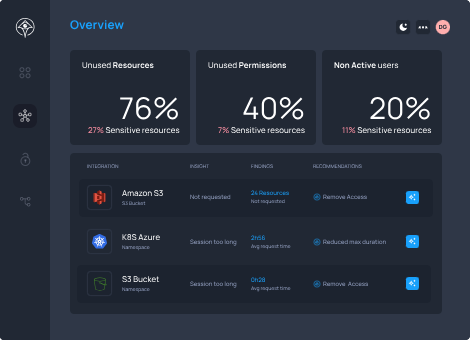
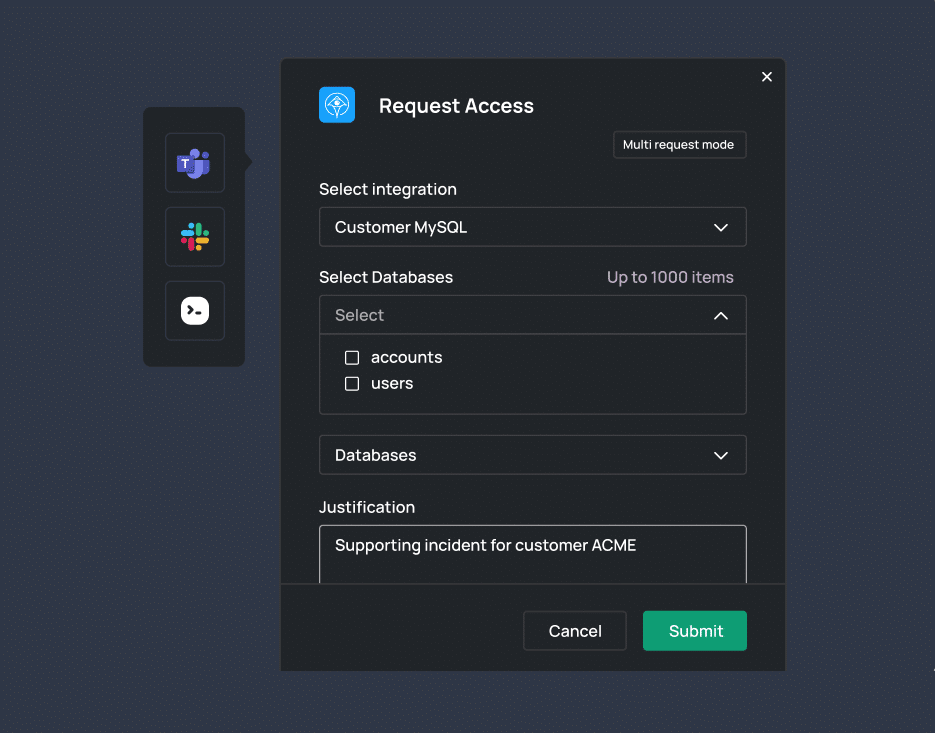
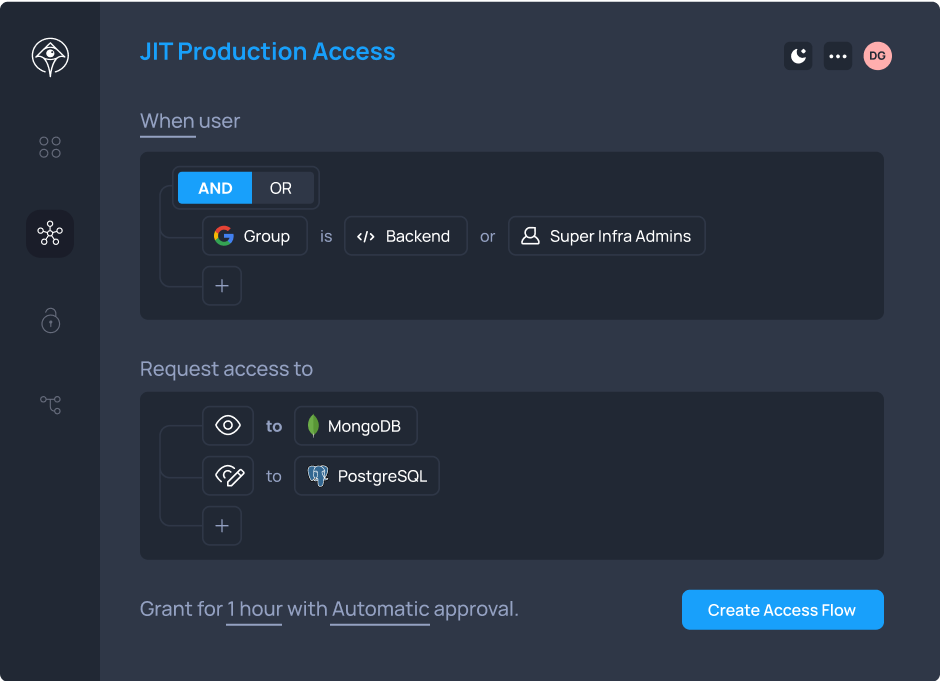
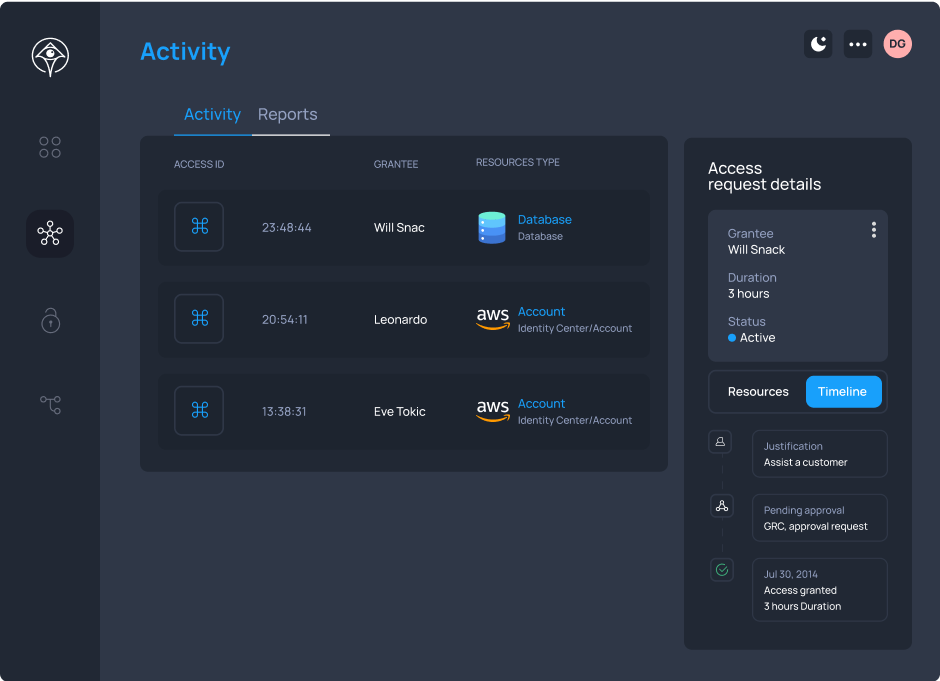
Apono replaces standing privileges by creating access dynamically at runtime — scoped to the exact need, enforced in context, and automatically revoked. One platform for humans, machines, and AI agents across your entire cloud and hybrid infrastructure.